How to Avoid Malicious Files with Double Extensions
Ever wondered why files have extensions and how they work? That file extension – usually comprised of three letters – is basically a way of letting the operating system or applications know what type of information the file contains. That way, only applications that know how to read the information within the file will do so.
While native Windows file extensions are usually limited to three characters (e.g. “exe”, “txt”, “dll”, etc.) separated from the file name by the dot (“.”) character, there are exceptions. For example, newer versions of the Microsoft Office suite have introduced four-letter extensions for files (e.g. “.docx”, “.pptx”, “xlsx”, etc.), while other applications may have more than four.
Regardless of the number of letters in a file extension, it’s important that users know the most common ones and how they work, as attackers can sometimes trick them into downloading and executing files that seem legitimate, but are not.
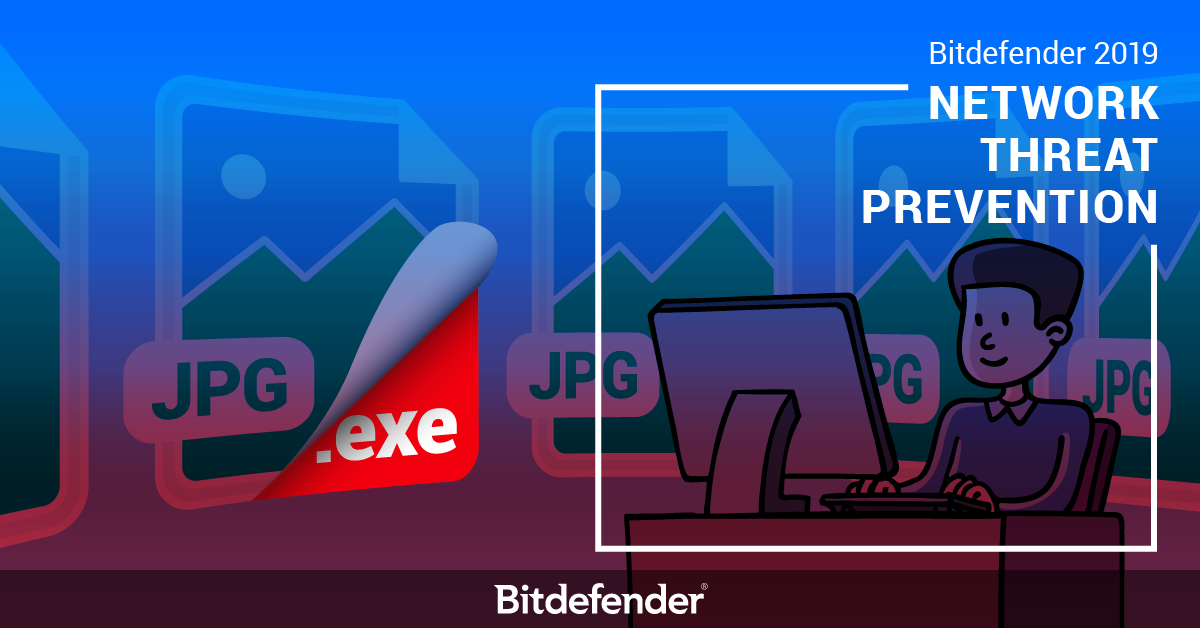
Attackers will usually manipulate file names, icons, and extensions to make a file look legitimate. For example, a file that looks like “example.jpg.exe” will often trick users into thinking it’s an image, when in fact it’s an application. That’s because the operating system usually doesn’t display the file extension – in this case “.exe” for known extensions. Users will only see the file name – “example.jpg” – which is in fact the file name. As you might have guessed, file names can include dots, which is exactly what threat actors exploit to their advantage. While this is a trivial example, we’ll dive a little deeper into how some file extensions can be used to deceive and trick users into executing various types of malware.
Bitdefender 2019 has introduced a new technology, dubbed Network Threat Prevention, designed to (among other things) spot threats that leverage this type of double-extension attack. It can also prevent vulnerabilities from being exploited, detect brute-force attacks on your passwords, prevent your system from being compromised in botnet attacks, and prevent personal and sensitive data from being broadcasted unencrypted.
However, let’s take a closer look at how Bitdefender 2019 Network Threat Prevention can help you steer away from threats that leverage double extension.
File Extensions 1 on 1
Modern Windows operating systems usually hide the file extension of widely popular files, because it’s far easier for users to rename files without having to constantly remember their extensions. However, that does present some problems when it comes to threats that abuse this feature.
You can think of files names and extensions as family members. Whenever the entire family gets together, everyone knows each other and you end up using their first names. For example, when you’re calling for your cousin John, you’ll will be calling “John” and not “John Smith”. Basically, the file name is “John” and the extension is “Smith.” Since you already know he’s part of the family, there’s no need to use – or in this case, display – the name “Smith”. It’s pretty much the same with file names and extensions. Known file extensions will often not be displayed.
Other operating systems, such as those based on the UNIX free and open-source operating system, even support multiple file extensions, indicating that the file may need to go through multiple transformations before becoming “readable”. For instance, “example.tar.gz” has two file extensions separated by the dot character, indicating that the file “example” is an archive comprised of several files (.tar) and that it’s compressed with an archiving library (.gz).
Windows files usually have one extension that’s separated by the file name using the dot (“.”) character. However, users are not supposed to always remember or know which file extension is associated to each application. This is why files are usually accompanied by an icon that makes it easier for the average user to know which application can open that file. For example, for text files that have the “.txt” file extension, the accompanying icon is a document with a couple of lines of code. Other examples include documents meant to be opened with the Microsoft Office Suite; documents have the “.doc” or “docx” file extension and the icon is usually a blue “W” on top of a document.
Visually associating file with their corresponding applications is now common in modern operating systems, which is why the ability to view file extensions is usually disabled by default. Unfortunately, hackers can abuse the fact that users don’t see the full file extension or the fact that they recognize the file’s icon and trick victims into downloading and executing malicious files that seem legitimate to the untrained eye.
No Shortcuts When it Comes to Privacy
Diving back to the “example.txt” scenario, what would happen if you automatically downloaded the maliciously renamed “example.txt.scf” file in your Downloads directory?
The “.scf” extension is a Windows Explorer Command (Shell Command File) that’s basically a shortcut file used to store and execute instructions involving file manipulation (e.g. copy, download, etc.). In a nutshell, files that have the”.scf” extension are automatically executed as soon as the folder they’re in is opened. All the user has to do is download the file to a folder and, as soon as he opens the folder, the instructions in the shortcut file will automatically be executed without the user’s knowledge.
Imagine ordering a pizza and waiting for the delivery guy. You get a knock on the door and you open up because you see someone holding a pizza box. As soon as he’s inside and waits for you to pay him, the pizza guy automatically starts looking around for valuables that you might have around. After you pay him and close the door behind him, you’ll find that, not only is the pizza box empty, but he also left with your watch and wallet.
The “example.txt.scf” double extensions example is pretty much the same. You expect to download a text file, when in fact it’s something completely different that could be rigged to “leave” with some of your personal data.
Because the file extension itself is benign, the instructions within those shortcut files could be dangerous to your system, especially if they’re automatically executed. The example of “.scf” files is particularly relevant as attackers have used them to steal Windows credentials. The file was maliciously planted on a website and as soon as users visited it, they would automatically download it. Once users visited the Downloads folder, the “.scf” file would automatically be executed and send the victim’s Windows password hashes and domain name to the attacker’s command and control server.
Where does Bitdefender step in?
Bitdefender has the ability to detect if an executable file with double extension tries to leak your private information, even if the true file extension is hidden from the user. Users prompted with the message “Privacy threat blocked” will also see the following explanation for what happened: “The file used a double extension to try to pass off as legitimate and trick someone into opening it, thus we blocked it”.
This is only one of the threats that Bitdefender 2019 Network Threat Prevention can protect you from — it can do so much more in fending off privacy-threatening malware. Stay tuned for more articles on how the new Network Threat Prevention technology – as well as other technologies – can protect your personal and private information and data from online threats.
tags
Author

Bogdan is living his second childhood at Bitdefender as director of threat research.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
3 in 5 travel-themed spam emails are scams, Bitdefender Antispam Lab warns
August 10, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks









